The most common email threats II.

November 19, 2019
In the first part of “The most common email threats” we’ve described phishing and spear-phishing attacks. Today we will look on the other threats.
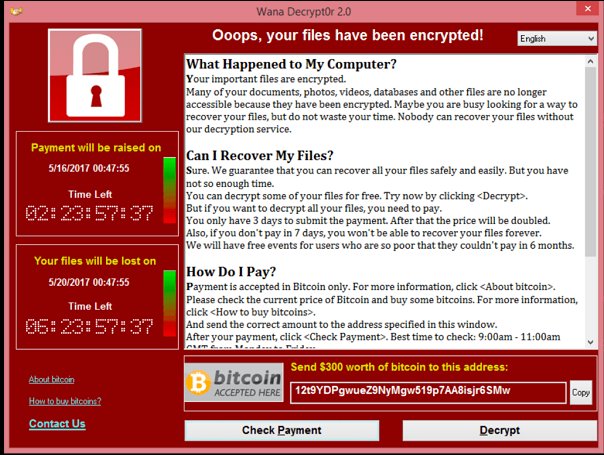
Ransomware
Ransomware is a type of malicious software (malware), that, once executed, will encrypt all data in your device. If you do not have backed up your data regularly, it seems that the only solution how to get your data back is to pay the ransom. Then, maybe, you will get your decryption key. We don’t recommend that, by paying the ransom you will support further attacks.
The attack starts with the email with a link, or attachment. The link will lead you to and infected website, that says: „Your computer has been seized because it contains illegal software or data. To unlock and pay the fine proceed to…”, or simply „Your data were encrypted. Pay the ransom.“
Unfortunately, ransomware infection is very complicated to solve, therefore ask a specialist for assistance, as he could get back your data and restore your device. However, the best protection is prevention and proper identification of the email, as we described here. And off course effective antivirus and antispam solution.
Picture source: Wikipedia
Spam
Spam is probably the most known email threat you can encounter. Basically, every unwanted email (such us advertisement etc.) is called spam, but also emails with viruses, malicious attachments, or links.
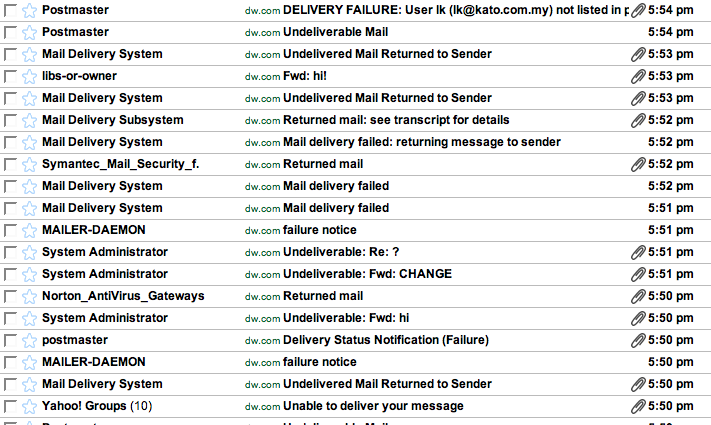
Spam alone could be dangerous as well. Big volume of spam could delay incoming important messages or block the whole email communication. This could mean considerable financial loss for the business.
Antispam Virusfree is able to stop spam and ensure no malicious emails reach your mailbox. Read more information about it here.
Photo by 1541 on Foter.com / CC BY-NC-SA